The IBM i platform gained great popularity at the end of the last century and is widely used now in various business areas due to its efficiency, reliability, and security. However, modern business requirements and IBM i digital transformation require more reliable data protection. In this article, we will talk about how IBM i security can be applied to applications and how to improve this using integrations.
How Secure is IBM i?
IBM i is an operating system developed for the AS400 line of systems (also known as IBM Power System, IBM System i). IBM first released this system in 1988 as OS/400 and since then constantly updated and developed it. Industries where security is one of the main priorities widely use IBM I. However, with the advent of new functionality, IBM i security issues are also emerging.
Since its creation, the operating system has offered 5 IBM i security settings so what are the advantages and weaknesses?
IBM i Security Advantages
- Level 10. A password is not required to enter a terminal session. This level does not provide security, so it has been removed.
- Level 20. Requires a password to log in, once logged in users will have access to all objects in the system.
- Level 30. Grants access rights to users at the object level.
- Level 40. Provides integrity protection and separates the user domain from the system domain. Configured by default on all IBM i devices.
- Level 50. Adds additional integrity protection features that meet the US Department of Defense’s “C2” security requirements.
IBM i Security Weaknesses
- Dangerous default security settings.
- Excessive user access.
- Patches and updates are poorly managed.
- Unverified permissions.
- Inadequate password management.
- Database vulnerabilities.
- Uncontrolled network access.
- Weak system audit.
For reliable data protection, you should use the highest security settings.
How Can IBM i Integration Improve Platform Security?
Integrations allow you to integrate data from IBM i applications with other ones both within the same system and in external systems. Software integration solutions can use end-to-end encryption to enhance data security. Although this ensures data security regardless of whether it is located in local or remote storage. Delimiting access rights and providing access to data only to those users who need it is an important way to guarantee data security. In this case, even if attackers steal the personal data of one of the users, they will be able to access only a very limited amount of information.
IBM i Security Applications with LANSA
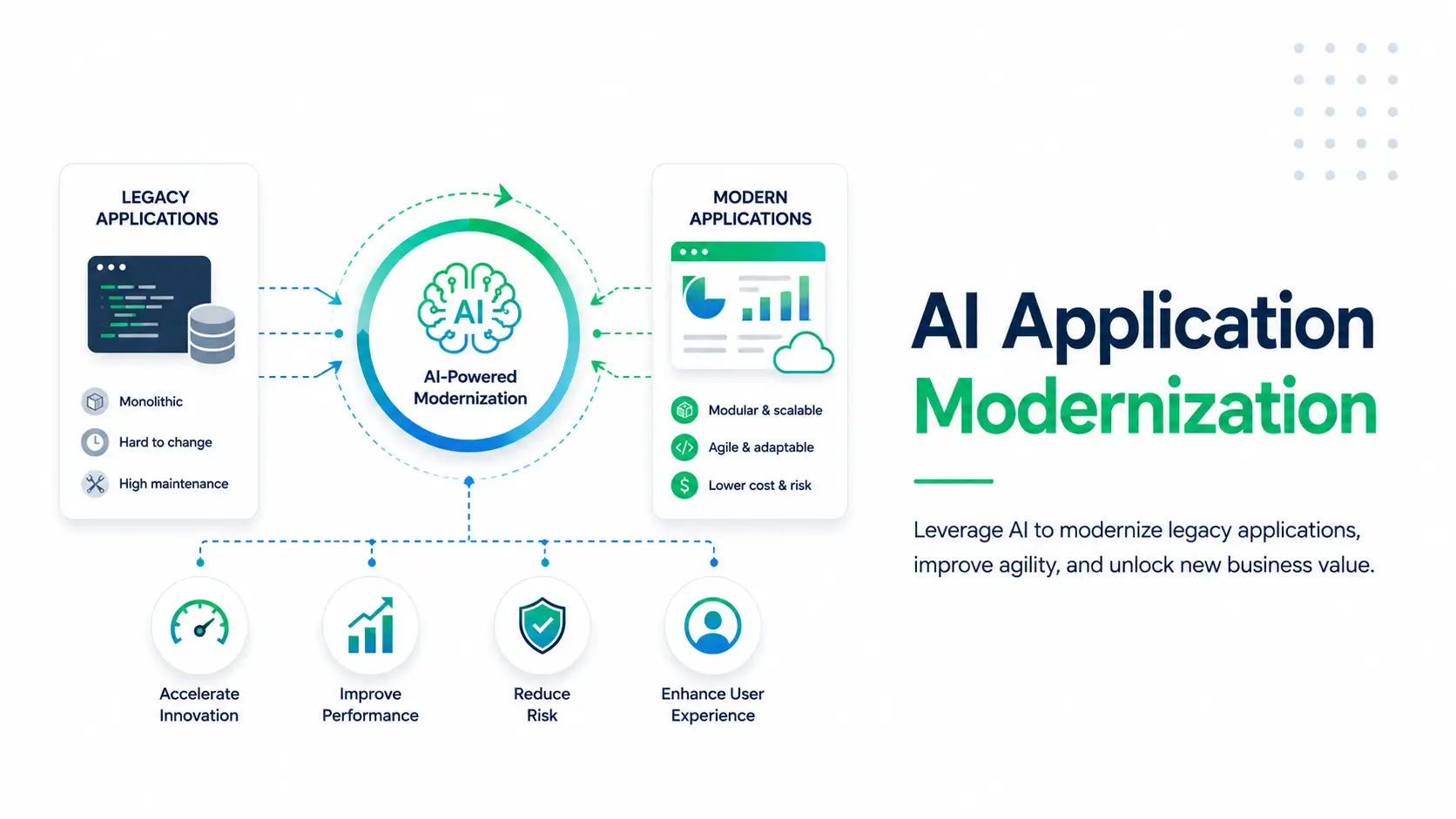
LANSA offers solutions to modernize your IBM i applications to ensure their security. Using modern technology will allow you to save a lot of time and money, as well as reduce the risk of a security breach.
Visual LANSA
Visual LANSA is a platform for rapid low-code application development. It allows software developers to create enterprise-level mobile, web, and desktop applications even without development experience. You can also deploy your apps to any device. Additionally, Visual LANSA offers tools specifically for the modernization of IBM i applications, which makes the process of modernization of any legacy system as simple as possible.
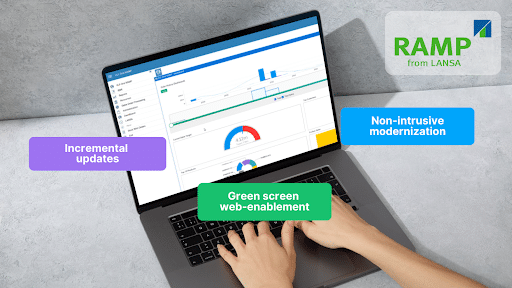
aXes
aXes is a tool that makes it easy to convert 5250 green screens into web-accessible mobile applications. It automates the process of creating IBM i 5250 web applications and converts existing 5250 screens to web pages out of the box without changing the source code. In addition, you can use aXes to simulate the actions of a human entering data on screens in a 5250 program. This allows you to integrate existing legacy systems with .NET, Java, or other 5250s without changing their source code.
Portalize
Portalize is a tool that allows you to easily create portals, without the need to code complex functions. It meets modern security standards and provides a high level of data security. Portalize offers a wide range of pre-built administrative functions that can be integrated into any application. In addition, you can easily configure the level of security and notifications for each user. Ready to start building secure applications with LANSA? Contact us and learn more about how to use LANSA for your business.
______________________________________________________________________
As well as our applications that improve IBM i security, we offer innovative technology in application development. Contact us to talk our team about requesting a free trial or see some of our case studies on how we’ve helped businesses across the world.